Multiple Updates below!
The Ontario Science Centre is a wonderful place in Toronto, a science playground for kids and even adults. I grew up going there and continue to visit every couple years. So I'm loath to cause them problems. A couple months ago (around March 25th) I emailed them through their "Contact Us" form to point out that their website is a complete security failure:
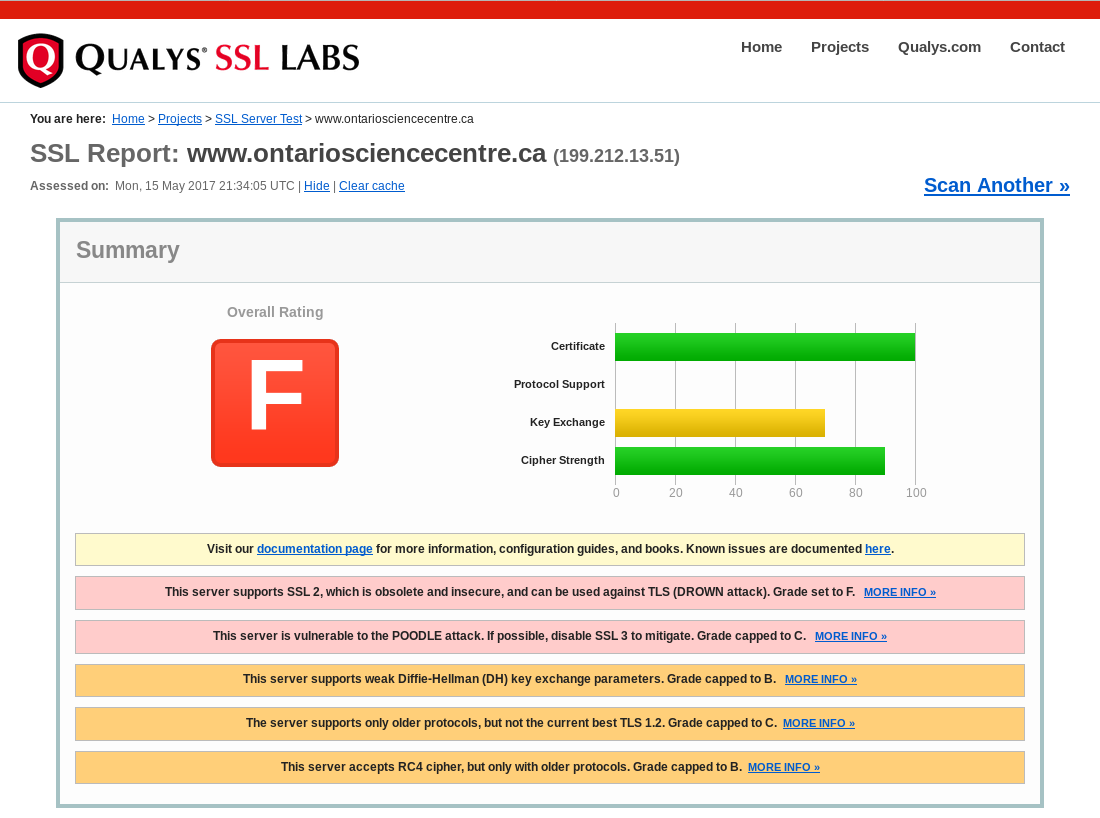
You can verify this yourself at https://www.ssllabs.com/ssltest/analyze.html?d=www.ontariosciencecentre.ca . (The Qualys SSL Labs SSL test is one of the best available right now.) The OSC's response to my email has been a resounding silence. I'm okay with them not answering me, but I'm NOT okay with them not fixing the problem. And since the problem persists, I'm going to raise a stink (on my blog, read by three people).
For those who don't follow SSL/TLS security (lucky you - if I didn't I'd find myself unemployed since I create secure websites for a living), this is pretty much as bad as it gets. Any competent website should be getting an "A," or a "B" at worst. Of course if you leave that site alone for six months there will probably be another spectacular security attack (like POODLE, mentioned in the image above) that compromises millions of sites, and your formerly A-rated site would now be drawing a "D" - that's just the way it goes. You have to keep working on this stuff.
While the term "SSL" is used to indicate a secure web site, the actual Secure Sockets Layer protocol from which the name is derived has been deprecated since June 2015. That sounds fairly recent, but in "Internet Time" it's quite a while. And when I say it was "deprecated," I mean that the last variant, SSL 3.0, was deprecated. SSL 2.0 (which the OSC still supports) was deprecated in 2011. These protocols aren't deprecated lightly: hundreds of thousands, possibly millions of websites rely on them and the people who issue the RFCs that deprecate these things know the problems deprecations cause. SSL was replaced with TLS - a protocol that's been around long enough to progress from version 1.0 to 1.1 and now the current version 1.2, and to have v1.0 be considered "weak." Case in point about deprecation: TLS 1.0 is considered weak, but it's not deprecated because it's too widely used: too many websites use it, too many older browsers can't support newer versions. So the standards bodies wait and hope that everyone will upgrade. When enough of them do, they deprecate the old standard.
Of course if you want to reassure yourself that the site is secure, you can find a link on the OSC site to their SSL provider who assure you it's completely safe ( https://www.entrust.net/customer/profile.cfm?domain=ontariosciencecentre.ca&lang=en ):
It looks really official, doesn't it? It doesn't mention that the OSC pays them a minimum of several hundred dollars a year, so they have zero incentive to tell you anything else. Most people won't look further than this: it all looks good, right? The site has a lock beside the URL and Entrust says it's okay.
This is a problem not only for people submitting their email addresses through the "Contact Us" form, but more importantly for people making ticket purchases with their credit card through the OSC's supposedly secure online form. It's particularly ironic and unfortunate given that the OSC is always promoting science education to anyone who'll listen ... and yet they ignore a computer science issue directly under their noses that has huge potential to cause financial harm to themselves and their customers.
Until they do something about this, please DON'T buy through the OSC's website.
Updates
2017-05-23:
I checked this morning, and their rating has gone up considerably:
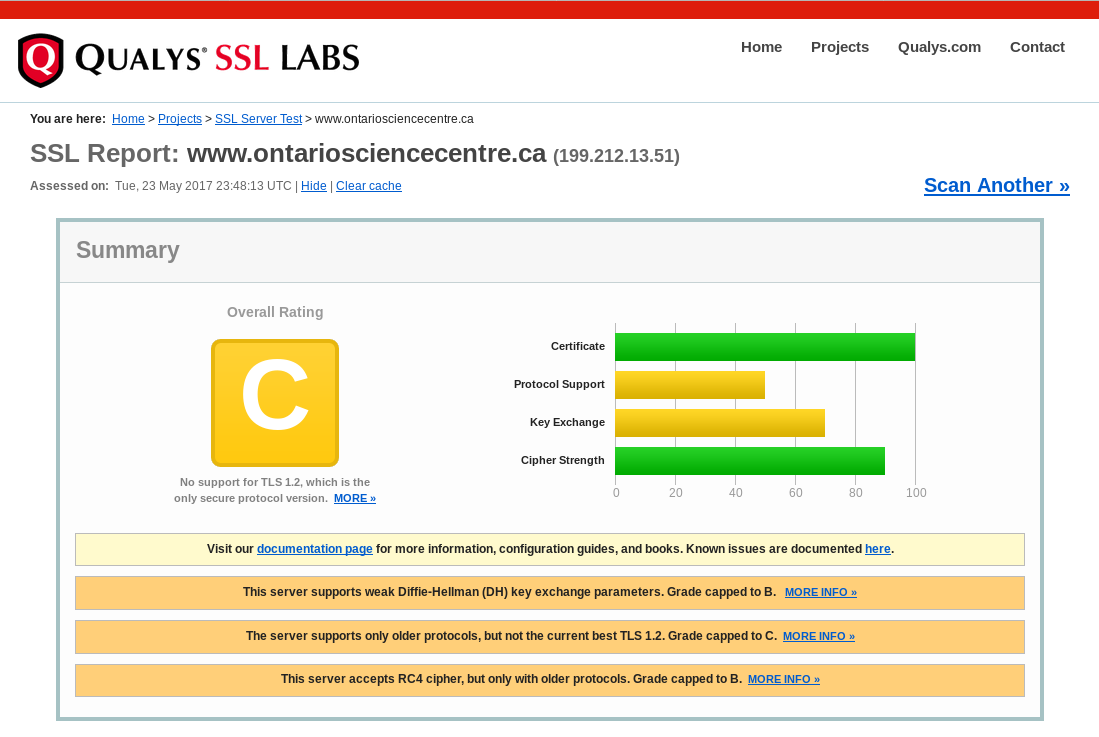
I hope they'll continue to improve.
2017-05-25:
And they're still working on it!
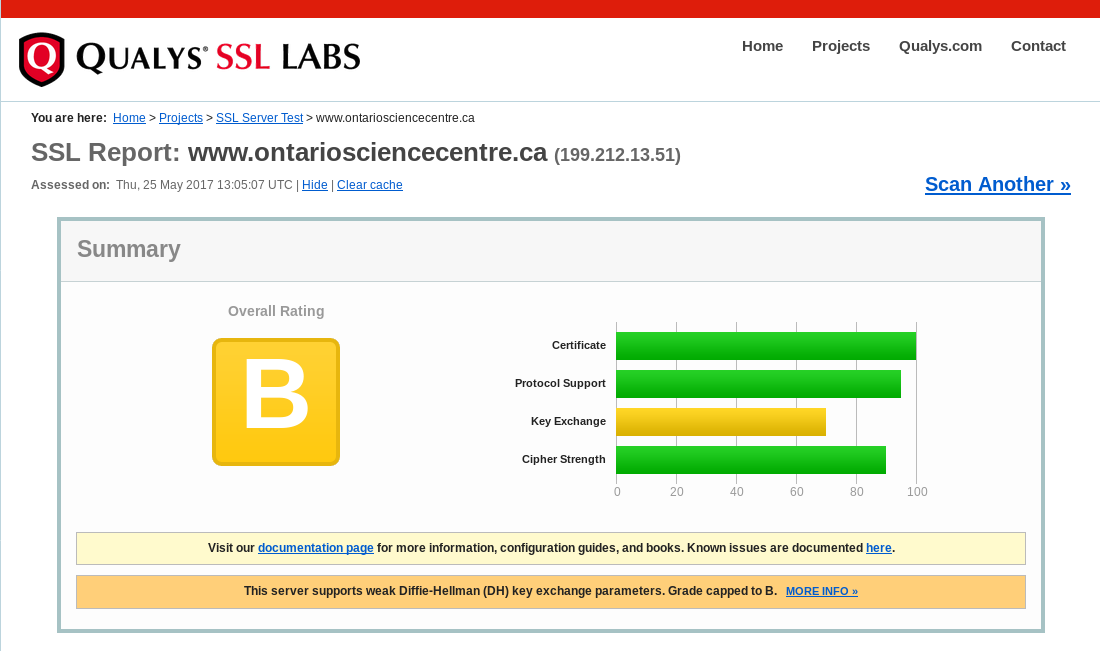
Generating your own Diffie-Hellman parameters is annoying, but not difficult.
2017-06-01:
This morning I got an amazingly polite email from someone at OSC (amazingly polite given what a pain in their asses I've been), apologizing for the delay in contacting me and thanking me for my help(!). So I immediately scanned their site again:
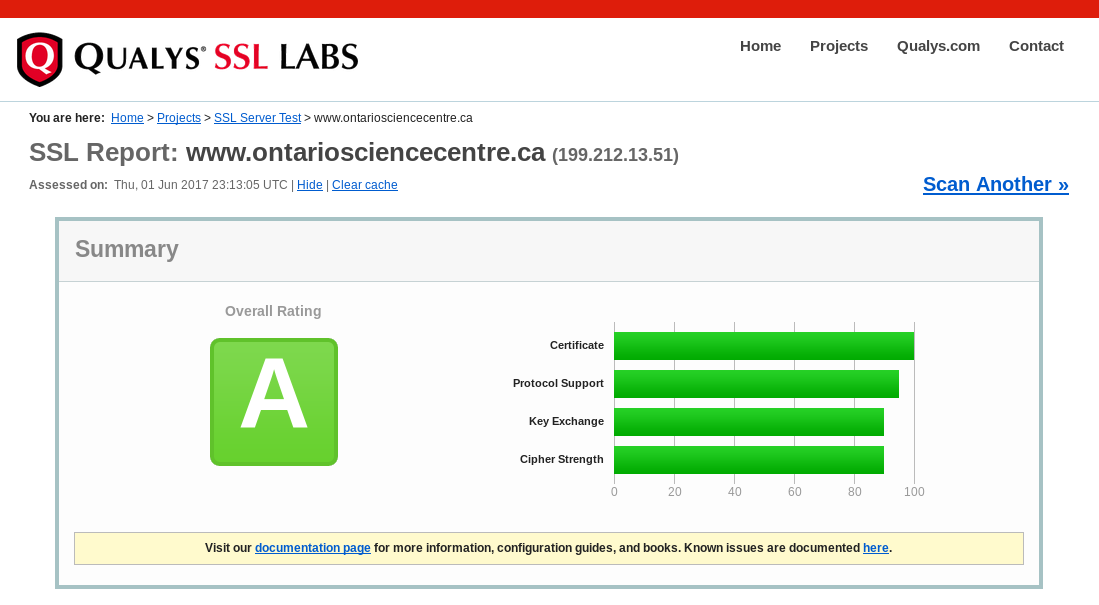
Great stuff!
If its any consolation to them, I know the pain they went through to fix this: I've been through it myself. Congratulations and thanks.