Nginx Cipher Suites
Giles Orr
Toronto Public Library
S5 Slide Show
- Wait! I can't see the contents of slide X!
- This is a S5 Slide Show
- the controls appear when the pointer is in the lower right corner
- select the "Ø" to get the print view (which will show everything on long slides)
- the print view will show you not only the contents of all slides, but also the speaker notes
- some of the speaker notes are simply for me, speaking to the audience - but much of it is elaboration on points made in the slides
Securing Your Web Server
- applies across Nginx, HAProxy, and (with a slight change of naming scheme) Apache
- Google is down-ranking non-encrypted sites
- Let's Encrypt certificates are free
- but - setting up an encrypted website is complex
- who here is directly or indirectly responsible for the running of a webserver?
- Let's Encrypt being free means that there's no longer a financial reason not to encrypt your website ...
- and when you add in Google's move to down-rank non-encrypted sites ... there are a lot of reasons to encrypt ASAP
- whatever certificate authority you use, research them: make sure they're not deprecated or rejected by browsers
SSL and TLS
- Secure Socket Layer (totally broken, don't use it)
- use Transport Layer Security
- but it's still called "SSL"
- TLS 1.0 is considered weak, but is still widely used to support old browsers
- TLS 1.3 is technically available, but as of today still infeasible
- the POODLE attack invalidated SSL3 completely in 2014
- you should support TLS 1.2, 1.1, and 1.0 in that order of preference
- TLS 1.3 only became an official standard in April 2018, and isn't properly supported by OpenSSL on Linux yet, which means ... it's not supported in any practical way yet
Your Web Server Configuration
- Nginx: ssl_ciphers
- HAProxy: ssl-default-bind-ciphers and ssl-default-server-ciphers
- Apache: SSLCipherSuite (naming is different)
- but cipher suites are ... volatile
- people are always trying to break cipher suites - both "white hats" (legitimate security researchers) and "black hats" (bad actors)
- a good example is RC4: it was formative in cryptography and the web, but is now quite broken
The Line
ssl_ciphers ECDHE-ECDSA-CHACHA20-POLY1305:ECDHE-RSA-CHACHA20-POLY1305:ECDHE-ECDSA-AES128-GCM-SHA256:ECDHE-RSA-AES128-GCM-SHA256:ECDHE-ECDSA-AES256-GCM-SHA384:ECDHE-RSA-AES256-GCM-SHA384:DHE-RSA-AES128-GCM-SHA256:DHE-RSA-AES256-GCM-SHA384:ECDHE-ECDSA-AES128-SHA256:ECDHE-RSA-AES128-SHA256:ECDHE-ECDSA-AES128-SHA:ECDHE-RSA-AES256-SHA384:ECDHE-RSA-AES128-SHA:ECDHE-ECDSA-AES256-SHA384:ECDHE-ECDSA-AES256-SHA:ECDHE-RSA-AES256-SHA:DHE-RSA-AES128-SHA:DHE-RSA-AES256-SHA256:DHE-RSA-AES256-SHA:AES256-GCM-SHA384:AES256-SHA256:AES256-SHA:!RC4:!3DES:!DES:!MD5:!PSK:!SRP:!DSS;
- as you can see - it is not your friend, and trying to understand it is a rabbit hole full of pain
- the structure is incredibly basic: a colon-separated list of cipher suites you want your server to use, terminating in a semi-colon
- every one of those acronyms should be researched
The Easy Way
- https://mozilla.github.io/server-side-tls/ssl-config-generator/
- use the "Intermediate" or "Modern" setting
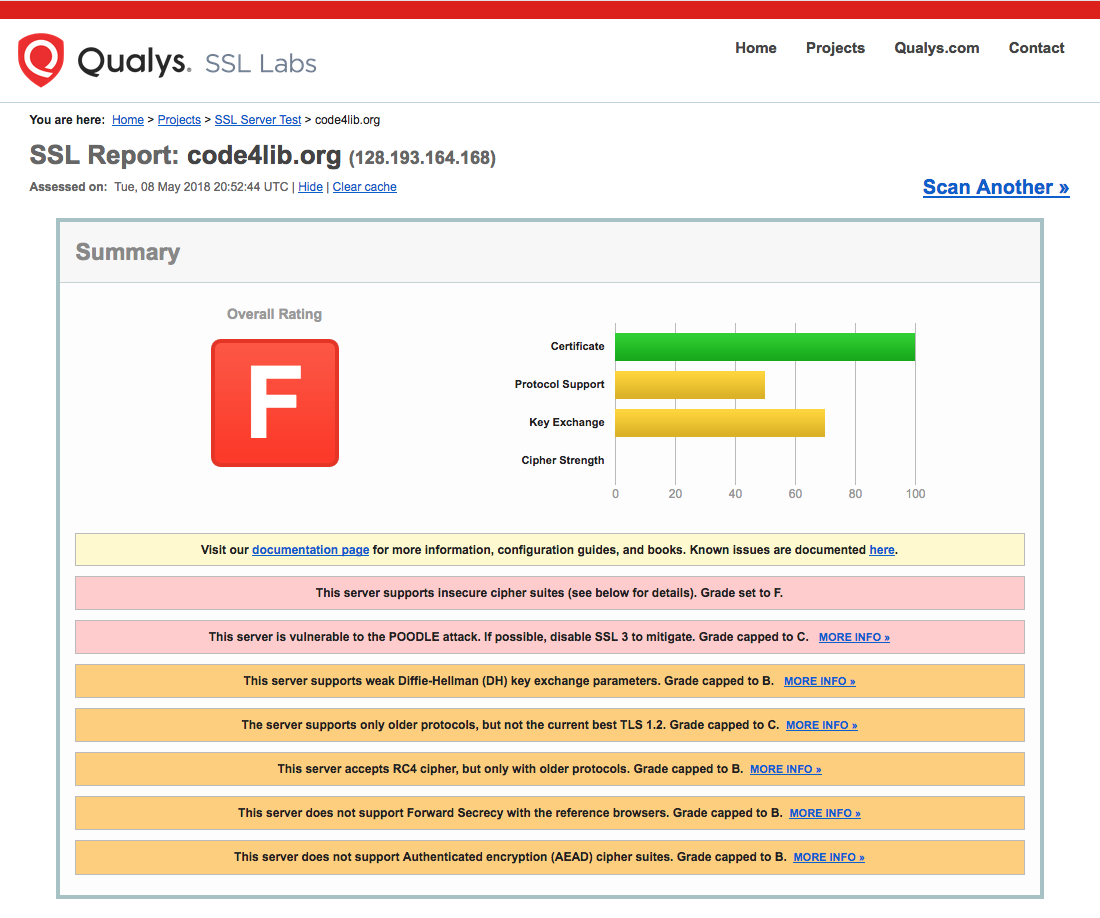
- test your site with https://www.ssllabs.com/ssltest/ (aka "Qualys") or equivalent
- I recommend doing your own cipher suite research, but using Mozilla's configuration generator is an option if you don't have the time right now
- "Modern" supports only very recent browsers - it's definitely more secure, but could lock out some of your users
- there are a number of sites to test your SSL/TLS configuration: I like Qualys best as it seems both most thorough and easiest to read of the ones I've seen
- and keep in mind that a configuration that's up-to-date and drawing an "A" score should be tested every couple months as those ciphers keep being broken and a winning config now can be invalidated by a research paper next month
- you MUST stay on top of it
Cipher Suite Breakdown
ECDHE-ECDSA-AES128-GCM-SHA256
- ECDHE - Key exchange
- ECDSA - Authentication
- AES128 - Cipher Algorithm
- GCM - Mode
- SHA256 - Message Authorization Code
- ECDHE - Elliptic-Curve Diffie-Hellman, Ephemeral keys
- ECDSA - Elliptic Curve Digital Signature Algorithm
- AES128 - Advanced Encryption Standard followed by a key size
- GCM - Galois/Counter Mode
- SHA256 - Secure Hash Algorithm, followed by a key size
Don't Use
- at the end of the cipher suite string: !RC4:!3DES:!DES:!MD5:!PSK:!SRP:!DSS
- That means: don't use these ciphers
- OpenSSL supports all these algorithms - for backwards compatibility or decrypting old stuff
- so we warn it off
- again, which ones you block are a matter of research ...
Algorithms and Ciphers (Reference)
- This is a reference slide: you can read it later
- 3DES = Triple Data Encryption Algorithm: "This can be considered broken, as the whole 3des keyspace can be searched thoroughly by affordable consumer hardware today (2017)." ( https://en.wikipedia.org/wiki/Triple_DES ). OpenSSL has deprecated the algorithm as of August 2016.
- AES128/AES256 = Advanced Encryption Standard followed by a key size, a NIST standard: "It supersedes the Data Encryption Standard (DES)." "At present, there is no known practical attack that would allow someone without knowledge of the key to read data encrypted by AES when correctly implemented." ( https://en.wikipedia.org/wiki/Advanced_Encryption_Standard )
- CAMELLIA256 = Camellia cipher: "a symmetric key block cipher with a block size of 128 bits and key sizes of 128, 192 and 256 bits." "Camellia is considered a modern safe cipher. Even using the smaller key size option (128 bits), it's considered infeasible to break it by brute-force attack on the keys with current technology." ( https://en.wikipedia.org/wiki/Camellia_(cipher) )
- CBC/CBC3 = Cipher Block Chaining: not strictly encryption, "each block of plaintext is XORed with the previous ciphertext block before being encrypted," which makes it very much harder to decrypt a message in pieces(?). CBC3 is an OpenSSL-only name, indicating the use of 3DES. ( https://en.wikipedia.org/wiki/Block_cipher_mode_of_operation#CBC )
- CHACHA20 = A variant of the Salsa20 stream cipher: "Google has [in 2015] selected ChaCha20 along with Bernstein's Poly1305 message authentication code as a replacement for RC4 in TLS." ( https://en.wikipedia.org/wiki/Salsa20#ChaCha_variant )
- DES = Data Encryption Standard: "This cipher has been superseded by the Advanced Encryption Standard (AES)." It's considered insecure. ( https://en.wikipedia.org/wiki/Data_Encryption_Standard )
- DHE = Diffie-Hellman Ephemeral key exchange: "a method of securely exchanging cryptographic keys over a public channel." Considered secure - so long as you generate your own DH parameters instead of using the defaults (and use a reasonable key size: we use 2048 because 4096 takes a really long time). ( https://en.wikipedia.org/wiki/Diffie%E2%80%93Hellman_key_exchange )
- DSS = Digital Signature Standard: I can't find out why this is deprecated, but there seems to be wide agreement on exactly that. ( https://en.wikipedia.org/wiki/Digital_Signature_Algorithm )
- ECDHE = Elliptic-Curve Diffie-Hellman, Ephemeral keys: "an anonymous key agreement protocol that allows two parties, each having an elliptic-curve public-private key pair, to establish a shared secret over an insecure channel." ( https://en.wikipedia.org/wiki/Elliptic-curve_Diffie%E2%80%93Hellman )
- ECDSA = Elliptic Curve Digital Signature Algorithm: there have been attacks against ECDSA, but they appear to have been related to specific bad implementations. However: "the trustworthiness of NIST-produced curves being questioned after revelations that the NSA willingly inserts backdoors into softwares, hardware components and published standards were made; well-known cryptographers have expressed doubts about how the NIST curves were designed, and voluntary tainting has already been proved in the past." ( https://en.wikipedia.org/wiki/Elliptic_Curve_Digital_Signature_Algorithm )
- EDE = Encrypt-Decrypt-Encrypt - not sure I understand this one, but it seems to be exclusively associated with 3DES, an algorithm you shouldn't use anyway.
- GCM = Galois/Counter Mode - "a mode of operation for symmetric key cryptographic block ciphers that has been widely adopted because of its efficiency and performance." ( https://en.wikipedia.org/wiki/Galois/Counter_Mode )
- POLY1305: "a cryptographic message authentication code (MAC) created by Daniel J. Bernstein. It can be used to verify the data integrity and the authenticity of a message." "The security of Poly1305-AES is very close to the underlying AES block cipher algorithm. Consequently, the only way for an attacker to break Poly1305-AES is to break AES." ( https://en.wikipedia.org/wiki/Poly1305 )
- PSK = Pre-Shared Key: not a useful/practical algorithm for a public web server ( https://en.wikipedia.org/wiki/TLS-PSK )
- RC4 = Rivest Cipher 4: "While remarkable for its simplicity and speed in software, multiple vulnerabilities have been discovered in RC4, rendering it insecure." (Wikipedia) ( https://en.wikipedia.org/wiki/RC4 )
- RSA = Rivest-Shamir-Adleman: an older algorithm, but - surprisingly - still considered secure ( https://en.wikipedia.org/wiki/RSA_(cryptosystem) )
- SHA/SHA256/SHA384 = Secure Hash Algorithms: SHA-1 (seen in Cipher strings as just "SHA") is considered insecure, while SHA-2 (the numbered values) is generally okay. ( https://en.wikipedia.org/wiki/Secure_Hash_Algorithms )
- SRP = Secure Remote Password: like PSK, not practical for a public web server ( https://en.wikipedia.org/wiki/TLS-SRP )
What You Need to Know
- each acronym represents a cipher algorithm and years of research
- Use the configuration generator OR lots of reading OR both
- TEST your server configuration
- not once, but at regular intervals, forever
- Or this is what happens: https://www.ssllabs.com/ssltest/analyze.html?d=code4lib.org&latest
- I needed a demo - I'm sorry it had to be code4lib ... but as of 2018-05-09 they're scoring an "F"
- Yes, I did try to notify them a couple weeks ago
- I found this because I set Firefox to not accept SSLv2 or SSLv3
- Firefox - about:config - security.tls.version.min - set to "2" (sets the minimum SSL to TLS 1.1)
- A more complete explanation: http://kb.mozillazine.org/Security.tls.version.*#Possible_values_and_their_effects
- Note that when you visit a site that only supports SSLv2 or v3, Firefox assumes you're wrong and asks if you want to reset to sane values: your call, but I'm sticking with my paranoia
Backup Screen Shot
Conclusion
- slides should be posted at https://www.gilesorr.com/blog/ tonight or tomorrow
- Kaitlin should be posting the slides on the Code4Lib site?
- Questions?